
‘GhostCringe’ Malware threatening Microsoft SQL and MySQL servers
Threat actors target poorly secured Microsoft SQL and MySQL database servers to execute GhostCringe remote access trojans on vulnerable devices. This interestingly named malware is also known as ‘CirenegRAT’ and is also a variant of Ghost RAT malware that was most recently deployed in 2020 Chinese cyber-espionage operations but dates as far back as 2018. In a new report published on the 16th or March 2022 by cybersecurity firm AhnLab, states that researchers outlined how hackers behind GhostCringe are targeting poorly secured database servers with weak account credentials and no oversight.
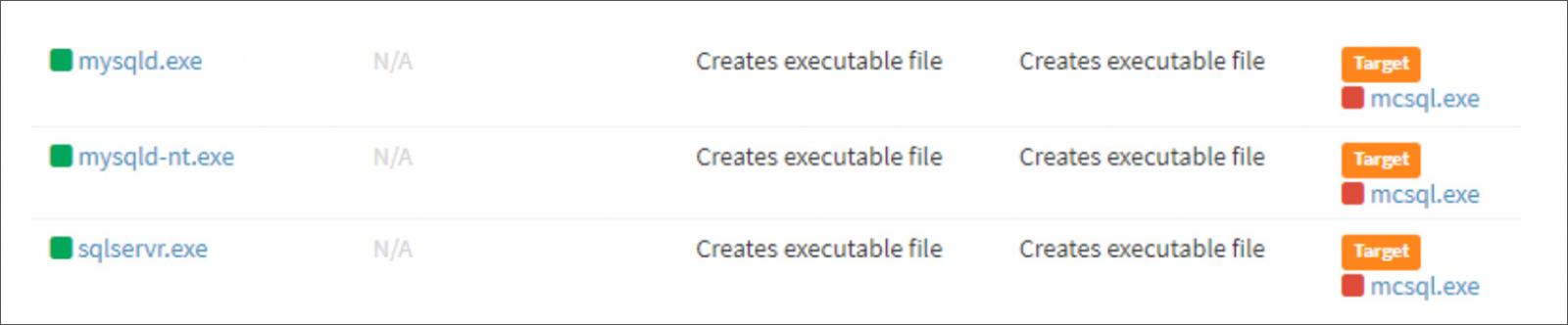
As it is evident below, the threat actors are breaching these database servers and using the mysqld.exe, mysqld-nt.exe, and sqlserver.exe processes to write the malicious ‘mcsql.exe’ executable to disk.
These malicious attacks are also similar to the Microsoft SQL server attacks that was reported last February, which dropped Cobalt Strike beacons using the Microsoft SQL xp_cmdshell command. Additionally, the report also mentions the presence of multiple malware samples on the examined servers, indicating competing hackers are breaching the same servers to drop payloads for their own campaigns.
GhostCringe entering the server
Gh0stCringe RAT is known to be a powerful malware that establishes a connection with the C2 server to receive custom commands or exfiltrate stolen information to the adversaries.
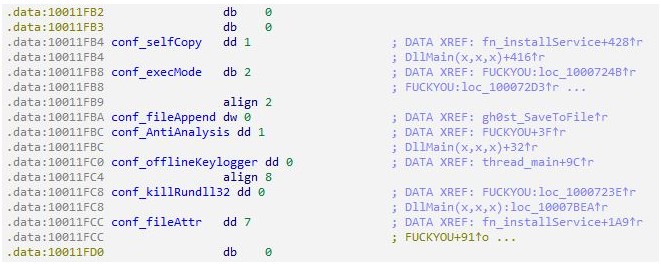
The malware can be configured during deployment with specific settings concerning its functions, as detailed below:
- Self-copy [On/Off]: If turned on, it copies itself to a certain path depending on the mode.
- Mode of execution [Mode]: Can have values of 0, 1, and 2.
- File size change [Size]: In Mode #2, the malware copies itself to the path ‘%ProgramFiles%\Cccogae.exe’, and if there is a set value, it adds junk data of the designated size to the back of the file.
- Analysis disruption technique [On/Off]: Obtains the PID of its parent process and the explorer.exe process. If it results in a value of 0, terminates itself.
- Keylogger [On/Off]: If turned on, the keylogging thread operates.
- Rundll32 process termination [On/Off] If turned on, executes ‘taskkill /f /im rundll32.exe’ command to terminate the rundll32 process that is running.
- Self-copy file property [Attr]: Sets property to read-only, hidden, and system (FILE_ATTRIBUTE_READONLY|FILE_ATTRIBUTE_HIDDEN|FILE_ATTRIBUTE_SYSTEM).
Of the above, the keylogger is maybe the most aggressive component as this is what steals user inputs from the compromised system. The keylogging component uses the Windows Polling method (GetAsyncKeyState API) for querying the state of every key through an endless loop. This otherwise reliable logging method introduces the risk of suspiciously high CPU usage, but in poorly managed servers, this is unlikely to cause problems to the threat actors. GhostCringe will also monitor the keypresses for the last three minutes and send them with basic system and network information to the malware’s command and control servers. These logged keystrokes will allow the threat actors to steal login credentials and other sensitive information that logged-in users entered on the device.
Modes and commands
CirenegRAT supports 4 operational modes, namely 0, 1, 2, and a special Windows 10 mode, selected by hackers during deployment.
The modes configure how persistence is established via the modification of the Windows registry and the activation of the self-copy module. For example, Mode #0 is running without persistence, while Mode #2 establishes persistence and considers self-copy settings.
As for the remote commands supported by the RAT, these are summed up in the following:
- Download additional payloads from the C2 and execute them.
- Connect to a URL via IE
- Destroy MBR (master boot record)
- Keylogging (independent command)
- Steal clipboard database
- Collect Tencent-related information
- Update
- Uninstall
- Register Run Key
- Terminate host system
- Reboot NIC
- Scan for running processes
- Display message pop-up
How can you secure the Database?
It is advised that you first update your server software to apply the latest available security patches, which helps exclude a range of attacks that leverage known vulnerabilities. It is also essential to use a strong admin password that is obviously hard to guess or brute-force. The most crucial and essential step is to place the database server behind a firewall allowing only authorized devices to access the server. Finally, monitor all actions to identify suspicious reconnaissance activity and use a data access controller for data transaction policy inspection.